Putting DNS Abuse into context.
Posted on 19 September 2020
We are currently working on a project to provide abuse monitoring information to our customers.
Giving our customers just the raw data is not helpful, so our goal is to contextualize the data.
We still have long ways to go, but the basics are there.
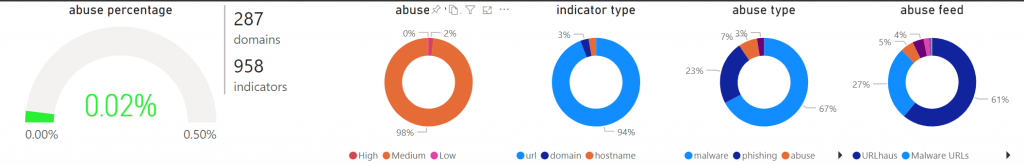
So what do I see right now on our platform?
- Malware (67%)
- Phishing (23%)
- The rest falls into somewhat general buckets like BEC fraud, DGA, botnets, dark lists, crypto mining, etc. Very low incidental percentages.
The above-mentioned data is from two years of monitoring.
On the left is displayed the overall abuse percentage since …